Assuming you already have an SSL/TLS key that you may have created for your HTTP server [Read It], we will use it for the VSFTPD.
sudo apt update sudo apt install vsftpd sudo service vsftpd status sudo ufw allow from 200.200.200.200 to any
For now, you should allow your public IP (replace 200.200.200.200 with yours) to have full access to your server to avoid any problem with the open ports on your firewall. Later we will remove this line and apply the precise ports.
Test connecting to your FTP server with FileZilla (for example). You might be successful. Now edit the configuration file:
sudo cp /etc/vsftpd.{conf,bkp}
sudo nano /etc/vsftpd.conf
Look for all of these configurations and make them look the same:
listen=NO listen_ipv6=YES anonymous_enable=NO local_enable=YES write_enable=YES local_umask=022 dirmessage_enable=YES use_localtime=YES xferlog_enable=YES connect_from_port_20=YES secure_chroot_dir=/var/run/vsftpd/empty pam_service_name=vsftpd utf8_filesystem=YES
For the SSL/TLS the configurations are (just add them at the end):
rsa_cert_file=/etc/apache2/md/domains/domain.com/pubcert.pem rsa_private_key_file=/etc/apache2/md/domains/domain.com/privkey.pem ssl_enable=YES allow_anon_ssl=NO force_local_data_ssl=YES force_local_logins_ssl=YES ssl_tlsv1=YES ssl_sslv2=NO ssl_sslv3=NO require_ssl_reuse=NO ssl_ciphers=HIGH
Note: for this tutorial we assumed the server already has the certificate issued by Let’s Encrypt using the module MD of Apache. If it was generated in another way, search for these files in your system or purchase them. If this is your case, they might located as described above and probably only the domain name needs to be changed.
You should also enable “Passive Mode” (recommended):
pasv_enable=Yes pasv_max_port=40000 pasv_min_port=50000
Restart the service and check it is running, and also test connecting to it from FileZilla:
sudo systemctl restart vsftpd sudo systemctl status vsftpd
Let’s remove that odd permission from your firewall and make it precise to your situation:
sudo ufw status numbered | grep 200.200.200.200
Remember that 200.200.200.200 is your own client public IP, not the server IP.
[ 7] Anywhere ALLOW IN 200.200.200.200
What we are looking for is the rile number to be deleted [7], in my case. Now, delete it (confirm when asked for):
sudo ufw delete 7
Add the new rules:
sudo ufw allow 20:21/tcp comment "FTP" sudo ufw allow 40000:50000/tcp comment "FTP Passive Mode"
The second line is for the case where you activated “passive mode”, and the range of ports (40000:50000) must match precisely between the VSFTP configuration file and the Firewall.
How wide should be the range? It is up to you!
In my case, I only use 50 because I don’t expect many multiple transfers. It depends on your server expected demand.
Let’s make the Fail2Ban monitor and protect this server. I am assuming you already have this service running [Read It], and you just need to include the VSFTP in the configuration:
sudo nano /etc/fail2ban/jail.local
Search for vsftpd (Ctrl+W), and it must look like this:
[vsftpd] enabled = true port = ftp,ftp-data,ftps,ftps-data logpath = %(vsftpd_log)s
Then go to the filter file:
sudo nano /etc/fail2ban/filter.d/vsftpd.conf
This is how it looks like, if different, just copy and paste to replace:
[INCLUDES] before = common.conf [Definition] __pam_re=\(?%(__pam_auth)s(?:\(\S+\))?\)?:? _daemon = vsftpd failregex = ^%(__prefix_line)s%(__pam_re)s\s+authentication failure; logname=\S* uid=\S* euid=\S* tty=(ftp)? ruser=\S* rhost=<HOST>(?:\s+user=.*)?\s*$ ^ \[pid \d+\] \[[^\]]+\] FAIL LOGIN: Client "<HOST>"(?:\s*$|,) ^ \[pid \d+\] \[root\] FAIL LOGIN: Client "<HOST>"(?:\s*$|,) ignoreregex =
Restart the Fail2Ban, check the status of the new Jail, and make one fail to attempt to log in to see if it captures the event.
sudo systemctl restart fail2ban sudo fail2ban-client status vsftpd
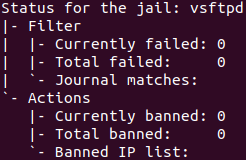
After the fail attempt, “Total failed” will start counting.
Just in case you ban yourself, issue the following command with your IP address in it:
sudo fail2ban-client unban 200.200.200.200
One Reply to “VSFTPD + TLS + Fail2Ban on Ubuntu 20.04”
Comments are closed.